IDF seeks to raise awareness on Hamas fake date apps
After army uncovers Hamas plot to lure soldiers with phony dating apps in effort to install spyware on their smartphones, IDF intelligence official praises soldiers outwitting the terror group by staying alert and reporting suspicious messages they had received; ‘Hamas did not do so well'.
The army uncovered on Tuesday the plot to spy on soldiers by befriending them on social media and then luring them into downloading fake dating applications that gave Hamas access to their smartphones.
Speaking to Ynet, Lt. Col. Y., head of the intelligence branch in the IDF's Information Security Department, praised the conduct of soldiers for reporting unusual messages they had received from girls tey did not know.
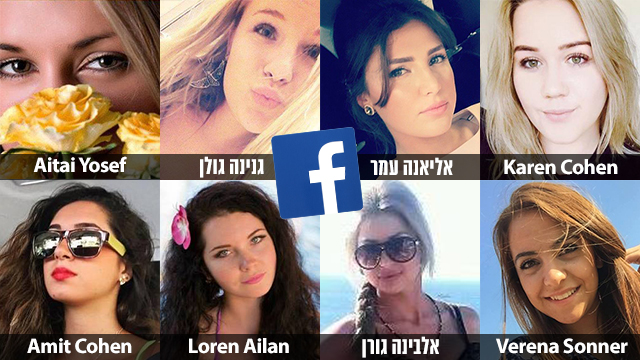
Hamas attempted to deceive the soldiers using fake messages sent by phony female profiles. The "girls" then attempted to convinced the troops to download malicious applications.
"We uncovered the plot thanks to the soldiers. If you remember, we identified a similar method in the January 2017 when the IDF uncovered that a Gazan terrorist group lures soldiers by using fake women's profiles before infecting their phones with spyware," Lt. Col. said.
"It was the same system, only this time we received dozens of reports from soldiers receiving unusual messages," she added.
Lt. Col Y. refused to say whether the application had been developed in Gaza. However, she noted that,"We know the (malicious) application was developed by Hamas. I cannot elaborate beyond that."
"We are talking about a young population that begins developing relationships precisely at these ages," Lt. Col Y. replied when asked how about the extent of the vulnerability of the soldiers between the ages of 18-21 to seduction attempts.
"Nevertheless, we understood (Hamas's attempts to lure soldiers into downloading malicious applications—ed) a year and a half ago and we are working hard to raise new awareness (on the matter)," Lt. Col Y. explained.
"We've seen their (Hamas's) attempts to reach out to all IDF soldiers and not only to combat soldiers. Its goal is to entice the soldiers to strike a conversation and then convince them to download an application that takes over smartphones," the officer elaborated when asked about the terror group's aim.
"Everything which is photographed, played, and conversations being held next to the phones—all of this information is something they want to gather," the intelligence branch head added. "I have to say they are not doing so well this time. We see a change in the soldiers' conduct."
Several other actions can be taken, Lt. Col Y. said when posed with the question of what a soldier can do to fight the new threat.
"First and foremost, when a woman reaches out to a soldier who he does not know he has to report it. If the woman continues sending messages in inaccurate Hebrew and the soldier does not succeed in setting a date with her, he should be suspicious," Y. said.
"If the conversation revolves around military matters, or if the woman asks the soldiers to download applications—applications from certain servers or from legitimate applications store—the soldier should become very suspicious and report it immediately," she urged.
Check Point Software Technologies' vice president Nitzan Ziv explained the dangers of downloading the pernicious spy applications.
"The minute the spy software is installed on a smartphone the attackers can hear everything that is going on in the room, have access to each file downloaded on the phone, activate the phone's camera and get the specific location of the phone," Ziv explained.
"Eavesdropping to a classified conversation and access to classified data can also be achieved (by this method)," he added.
"We witness similar phenomena in the business world as well where information about competitors can be obtained by simply using applications," Check Point's vice president continued.
Ziv noted that the Glancelove and Winkchat applications developed by Hamas to spy on IDF soldiers were of a high quality and reliable. "(Their) activity was smooth and almost undetectable. The application seemed good, professional, it had real content and was relevant to the World Cup games taking place in Russia," he said, adding that "The chance of a soldier looking at it and saying it's a problematic application is not high."
When asked how soldiers can detect problematic applications, Ziv replied that, "Beyond awareness, automated tools are also required since those things (malicious applications) are hard to detect.
"We are talking about a sophisticated fifth generation cellular offensive in which the place one begins is not where one ends," the vice president explained.
"The user can't really detect the applications by himself. Don't install applications with merely 500 downloads—they should raise suspicion as well," he recommended.