#OpIsrael cyber campaign sees limited success
Cyber intelligence analysts at SenseCy say many of the e-mails, credit card numbers leaked were recycled from past campaigns.
On April 7, 2015, hacktivist groups from around the Muslim world, from Indonesia to Morocco, tried to attack Israeli websites, particularly those of government institutions, as part of the #OpIsrael cyber campaign. This was the third round of the anti-Israel cyber campaign led by the Tunisian hacker group AnonGhost.
According to cyber intelligence analysts at SenseCy, despite all the publicity prior to the campaign, the hackers’ successes were limited to defacing several hundred private websites and leaking the email addresses of tens of thousands of Israelis, many of them recycled from previous campaigns. Several dozen credit card numbers were also leaked on information-sharing websites, but according to SenseCy's analysts, some were recycled from past leaks.
AnonGhost, which initiated the campaign, was the main actor behind it. However, other groups of hackers, such as Fallaga, MECA (Middle East Cyber Army), Anon Official Arabe, and Indonesian and Algerian groups also participated in the attacks. As the campaign progressed, we saw an increasing number of posts and tweets about it (over 3,000), but this is still significantly less than last year, when there were tens of thousands.
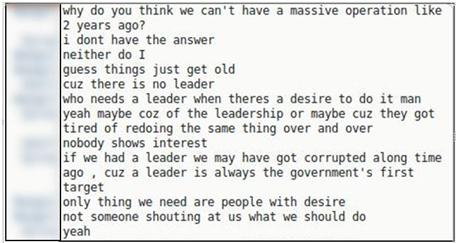
The campaign was conducted primarily on social networks, especially Facebook and Twitter. IRC (Internet Relay Chat) channels opened for the campaign were barely active, partly because hackers feared spying by “intelligence agents.” On closed forums and Darknet platforms, SenseCy's cyber intelligence analysts saw no activity related specifically to #OpIsrael.
All in all, according to SenseCy, we have not witnessed a dramatic change since the previous #OpIsrael campaigns, and mainly unprotected websites suffered from the attacks waged by pro-Palestinian hacktivists. Moreover, the number of authentic dumps containing email addresses, passwords and personal details was lower than the last campaign.
SenseCy is an Israeli-based cyber intelligence company focused on delivering effective CTI (Cyber Threat Intelligence). Its intelligence operations based on strong and unique Virtual HUMINT™ (Human Intelligence) capabilities, delivering actionable and relevant intelligence to various customers. SenseCy provides human-curated intelligence to financial institutions, corporate businesses, governments and corporations.