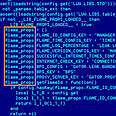
Flame-corrupted data
צילום:מעבדות קספרסקי
'Flame sought confidential Iranian blueprints'
Kaspersky Lab experts say sophisticated malware that hit Iran was after top secret mechanical, electrical designs related to nuclear program
Researchers at the Kaspersky Lab said Tuesday that one of the Flame virus' main objectives was to copy confidential technical drawings pertaining to Iran's secret military and nuclear facilities.
"Flame" hit Iran in late may and has since been hailed as "the most sophisticated cyber-bomb to date."
Related stories:
- Book links US to cyber-attacks on Iran
- IDF says 'defined essence of cyber warfare'
- Powerful cyber weapon found in Middle East
Tehran said it was able to contain the malware, but had admitted that significant amounts of data have been corrupted.
According to the BBC report, the hackers controlling Flame "used a number of complex fake identities in order to carry out their plans."

Kaspersky Lab (Photo: MCT)
Kaspersky's researches said that the fake identities – complete with fake addresses and billing information – were "used to register more than 80 domain names used to distribute the malware."
Researchers were also able to put together statistics on the extent of the Flame strike. The information was gathered via "sinkholing."
- For more on the raging cyber war click here
Vitaly Kamluk, a senior researcher at Kaspersky, explained that, "Sinkholing is a procedure when we discover a malicious server - whether it is an IP address or domain name - which we can take over with the help of the authorities or the (domain) registrar.
"We can redirect all the requests from the victims from infected machines to our lab server to register all these infections and log them," the BBC quoted him further.
Kamluk added that the attackers had a "high interest in AutoCad drawings, in addition to PDF and text files"; further cementing reports suggesting the Flame was on a complex reconnaissance mission.
"They were looking for the designs of mechanical and electrical equipment," Prof. Alan Woodward, from the University of Surrey, told the BBC.
"However, Iran isn't likely to have any intellectual property not available elsewhere. So, this suggests more a case of intelligence-gathering than onward selling on the black market," he added.
The origin of the cyber-attack is still unknown. Iran blamed Israel and the United States for the strike.
According to the report, an analysis of the malware's command and control centers (C&C) indicated that they were hosted in a variety of locations and are moved regularly. Such C&C centers have so far been detected in Hong Kong, Turkey, Germany, Poland, Malaysia, Latvia, Switzerland and the UK.
- Receive Ynetnews updates directly to your desktop










