Is Iran behind recent cyber attacks on Israel and EU?
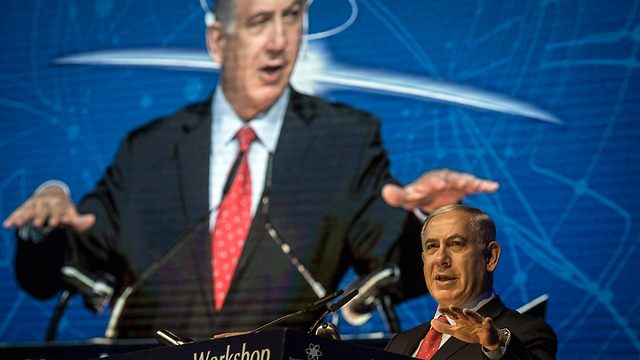
צילום: AFP
Iran could be behind state hacking campaign, Israeli cyber firm says
Recent cyber attacks on Israel, EU military targets perpetrated by state that misused US-made security software to lead attacks; 'they don't have their own capabilities,' expert says.
A previously undisclosed hacking campaign against military targets in Israel and Europe is probably backed by a country that misused security-testing software to cover its tracks and enhance its capability, researchers said.
The attack program relied on software usually sold by Boston-based Core Security to companies and other customers that want to test their own defenses, said researchers coordinated by Israel's independent Computer Emergency Response Team, or CERT.
The researchers from CrowdStrike and startup Cymmetria will present their unusual findings at the annual Chaos Communication Congress security conference in Hamburg on Saturday.
Criminal hackers have made use of penetration-testing tools such as Metasploit for years, other experts said, but most major government-sponsored hacks have specially written tools supplemented by free and widely available programs. That is in part because commercial programs could be traced back to specific customers.
Over time, however, the exposure of campaigns relying on the same tailor-made tools have made it easier for investigators to attribute those attacks to a specific government.
Using the Core Security program, which typically costs $10,000 or $20,000, could help muddy the waters, and CrowdStrike analyst Tillmann Werner said it could also help a second-tier cyber-power skip some of the work frequently undertaken by China, Russia and the United States.
"The most likely answer is they didn't have the capability to do it on their own," Werner said of the hackers, adding that "there is no risk of leaving tool-marks."
Werner and Cymmetria Chief Executive Gadi Evron, who also chairs the Israeli CERT, said they did not know who was behind the campaign.
But Evron said that one suspect would be Iran, judging by the victims and other evidence. The researchers dubbed the new campaign Rocket Kitten, following CrowdStrike's convention for naming all suspected Iranian hacking groups as Kittens.
Iran has beefed up its Internet operations in the years since its nuclear program was attacked by Stuxnet, an unusually destructive virus developed by the United States and Israel.
Evron said the team had uncovered seven connected attacks so far since April, including attempts to steal information from an Israeli company "adjacent to the defense and aerospace industry," an Israeli academic institution, a German-speaking defense agency, and an Eastern European defense ministry. At least the Israeli attempts failed, he said.
The attacks typically began with carefully targeted emails with Excel spreadsheet attachments sent to top executives. The recipients were prompted to allow a type of miniature program known as macros to run inside the Microsoft Corp spreadsheets, and if they agreed, malicious software would install. That software would download part of Core's Core Impact tool, the researchers said.
Core's licensing terms forbid use of its program against unsuspecting third parties, and Core Vice President of Engineering Flavio de Cristofaro said the company had not heard of such misuse in at least five years.
De Cristofaro said the company would assist the CERT if asked and in any case would try to track down how the software was pried away from the watermarks and other technical restrictions designed to limit its spread.
"We will follow that down," de Cristofaro said.