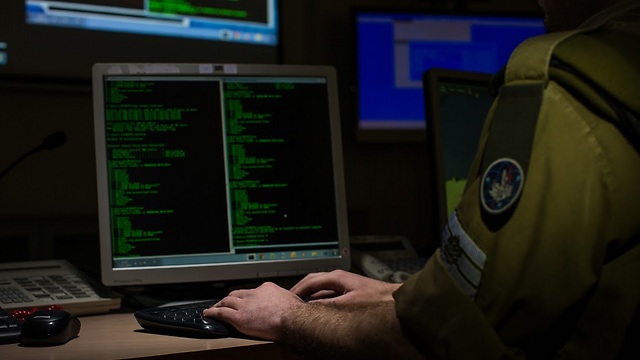
Idf's Cyber Division
צילום: דובר צה"ל
Defense: the most important challenge in cyberspace
Op-ed: The director of the Cyber Security Program at the INSS writes that one thing needs to be clear to anyone who heads a security organization: Defense is the key to everything.
The latest publications about the group calling itself the Shadow Brokers and its break-in of the National Security Agency’s computers are troubling officials in the United States. The group claims to have stolen classified malware codes, used at least until 2003, with which the NSA managed to penetrate and spy on foreign governments and organizations. The group is now offering to sell the codes for the fantastical amount of one million Bitcoins, currently worth upward of half a billion dollars.
The target of the break-in was the servers of Equation Group, a company linked to the NSA. Last week, in a series of tweets to his Twitter account, Edward Snowden hastened to note that this exposure might have dire political ramifications should it emerge that the NSA used the codes to spy on US allies and friends.
This is the nature of the beast. Espionage agencies, such as the NSA, have one main mission: to collect and provide high-grade intelligence for a wide array of state needs. In recent decades, there has been a real revolution in the processes and tools used in intelligence gathering, a revolution linked to two phenomena.
The first was the technological development in cyberspace, which meant a significant shift of intel gathering efforts from more traditional means to cyberspace. The second was the information revolution and distribution, and the possibility—which caused the need—to gather wide-ranging intel from all traffic, servers, computers, and end devices in cyberspace, in order to use sophisticated analytical tools to extract relevant intelligence.
But these phenomena also made intelligence organizations vulnerable in new ways. Cyberspace is not the sole hunting grounds of espionage organizations. It is also the very space where sophisticated hackers, motivated by a range of reasons, roam free. Thus, intelligence organizations find themselves having to invest huge effort into defending and securing their information and sources.
The challenge grows because cyberspace provides significant advantages to attackers over defenders. Suffice it to note the advantage of the attacker over the defender, as it is the former who chooses the time, location, and method, not to mention the fact that so far adequate defensive capabilities capable of withstanding unknown malware codes have yet to be invented. This advantage requires defenders to invest tremendous resources to protect their core assets.
These insights require intelligence organizations, and all other security agencies that gather and attack in cyberspace, to allocate significant attention and resources to defense. To make this a little more concrete, the assessment is that, because of the critical nature of the threat, resources devoted to defense should be no less than 60 percent of the total, whereas only 40 percent of the total resources should be going toward gathering and attack missions. This is a very conservative estimate.
It is unclear what actually took place in the last break-in, and how the secret codes were stolen from the NSA-affiliated Equation Group’s servers. But one thing must be clear to anyone heading a security organization: defense is the key to everything, whether we’re talking about security agencies around the world or those of the IDF and the intelligence community’s agencies in Israel. The traditional ethos of these organizations has always privileged the attack and intelligence gathering. The results are quick in coming, and the gratification is great, compared with the dry, dreary, hard-to-measure efforts of defense.
Defense is the core of the problem. Decision-makers will do well to pay the necessary attention to it, and provide the commensurate resources to protection, which is the central challenge at this time.
Col. (res.) Gabi Siboni, PhD, is the director of the Cyber Security Program at the Institute for National Security Studies (INSS) at Tel Aviv University.