Israel's National Cyber Directorate warned Monday of a suspected breach into Israeli dating websites and added that users' information might have been stolen. This is not a new phenomenon; some of these websites often include sensitive information such as sexual preferences, photos, and personal and intimate details about the user's life.
More stories:
Almost a decade ago, hackers breached the Ashley Madison dating website for married couples seeking affairs. The result was dramatic for many users who were exposed as unfaithful across the internet after refusing to pay extortion fees, or just to embarrass the dating website.
4 View gallery


Several Israeli dating sites have been breached by hackers recently
(Photo: Shutterstock)
A more recent case involved a breach into an Israeli dating website for the LGBT community, causing embarrassment for some users. It's not uncommon for hackers to exploit stolen information on such websites and attempt to blackmail users, for example by sending them emails and demanding payment.
If you assume that once it's done it's in the past, you'll be mistaken. Personal details and sensitive information can always be used by criminals, even if you've moved on. What do they do with them? They can exploit your usernames and passwords on other websites, for example, or try to use your information for various dubious purposes, ranging from applying for online loans to booking flight tickets or making purchases.
In the digital age, our personal information is one of the most valuable assets we have. It grants us access to various services, applications and websites, but at the same time, it can also be the most vulnerable aspect of our digital lives. When our personal information leaks or is exposed, the consequences can be catastrophic – from breaches of privacy to compromised bank accounts and even financial fraud.
Among the dating websites exposed in Monday's cyberattack were one for dating for married couples, another one for same-sex dating, a site for the religious community, and another for dating between wealthy individuals.
In any such website, the potential damage to one's reputation, wealth or family is enormous. With the assistance of cybersecurity company ESET, Ynet has compiled a few tips that could minimize the potential damage caused by such attacks, and in some cases even gain your information back.
4 View gallery


When our personal information leaks or is exposed, the consequences can be catastrophic
(Photo: Shutterstock)
1. Pay attention to the online services you use - follow news related to them. If you're somewhat tech-savvy, set up an alert that triggers when the name of the service is mentioned in headlines. Also, pay attention to emails you receive from a company that you know has fallen victim to an attack or data breach.
For example, if you have an account on a website that has just been revealed as breached and you receive an email from it asking for additional information or payment to prevent leaking the information, do not respond without consulting a qualified source like the National Cyber Directorate.
2. Change your password quickly - for both the service that suffered a data leak and all other sites. If it's a password you frequently use, you'll have to go through each site and change them one by one. Online criminals who gain access to data like usernames and passwords can try to use this information to access other services and websites you use.
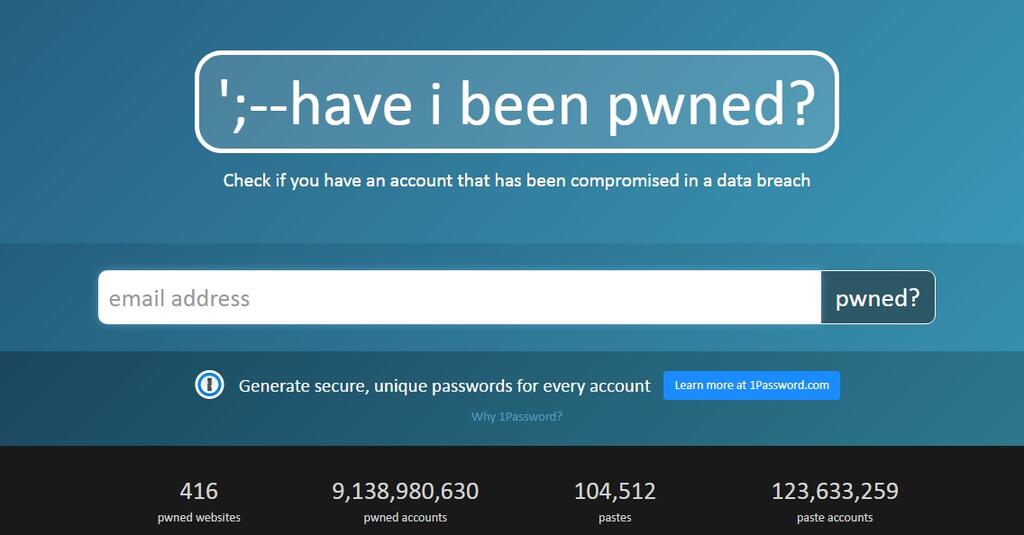
3. Check if your information has been leaked - the haveibeenpwned website collects a list of data breaches, and you can use it to check if your login details for a specific site have been compromised. Enter your email address in the search field to receive details about whether your information has been compromised.
Note that sometimes the site takes time to update, so if you suspect you were affected by a specific data breach, verify that the site has indeed updated its data about it. If you discover that your information has indeed leaked, there's no need to panic, but it's strongly recommended to change and refresh the passwords used in the affected sites.
4. Pay attention to your credit card statements - If you know that your credit card details have been compromised, it's safer and simpler to just cancel it. While it might not be pleasant, it's definitely better than attempting to control the damage after money has been stolen from your account.
If the situation isn't severe and there's no significant suspicion regarding your credit details being leaked, it's always advisable to monitor your credit card charges to avoid any surprises. Also, check with your bank if they've attempted to extract this information from you.
Additionally, keep an eye on other financial or health-related services, starting from national insurance, health care providers, insurance companies, and even transportation charges. For example, someone might use your information to forge a driver's license and then use it to pay toll road charges.
5. Protect your information better - use a strong, unique password for each website and service you use, and avoid using the same password for different services. This ensures that in case of a leak from one service, it won't serve as an entry card for your other accounts and services. Use password management software that allows you to generate unique passwords and requires you to remember only one password.
Enable two-factor authentication - In addition to your password, you'll need to enter a code sent via SMS or email. This way, even if a potential hacker has your username and password, they won't be able to break into your account without the code.
With all the tips we've provided, the most important one is not to wait. Don't wait to hear about a data leak in order to protect your information. Taking action today will save you from harm tomorrow. This is your own personal information and money.