Israeli online shoppers beware! Hackers based in China and Pakistan are presently conducting a broad phishing operation with the aim of pilfering personal information and credit details from users and shoppers on e-commerce websites of renowned brands. The Israeli cyber firm, Cybereason, uncovered this Chinese-led endeavor.
Read more:
As per the disclosed information, this advanced operation is set up to ensnare unsuspecting shoppers seeking to buy affordable clothing items and brands. The period of shopping holidays is a typical window for hackers and digital criminals to initiate such schemes. However, the focus on the Israeli audience in these campaigns is unusually specific and quite infrequent.
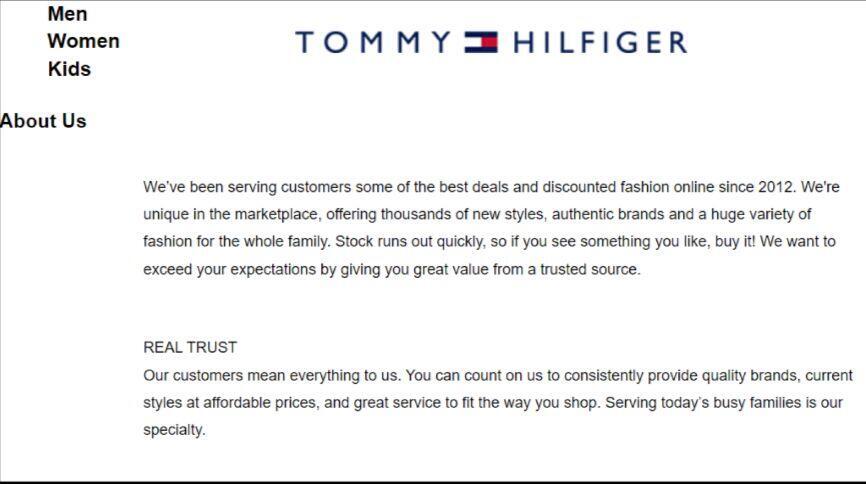
While the Chinese hackers show a commendable effort in their sophisticated mimicry of brand websites, the real masterstroke is delivered by their Pakistani counterparts. They've painstakingly copied a popular British shoe brand's website, creating an almost indistinguishable mirror image. Casual web surfers may find it extremely difficult to realize they're on a counterfeit site.
Notably, the Pakistani website has been fully translated into Hebrew, barring the shoe model names. This differs from the Chinese websites, which are entirely in English. Interestingly, when it comes to the URL - the origin of the domain - the Pakistani website doesn't even attempt to disguise its source, proudly displaying its roots.
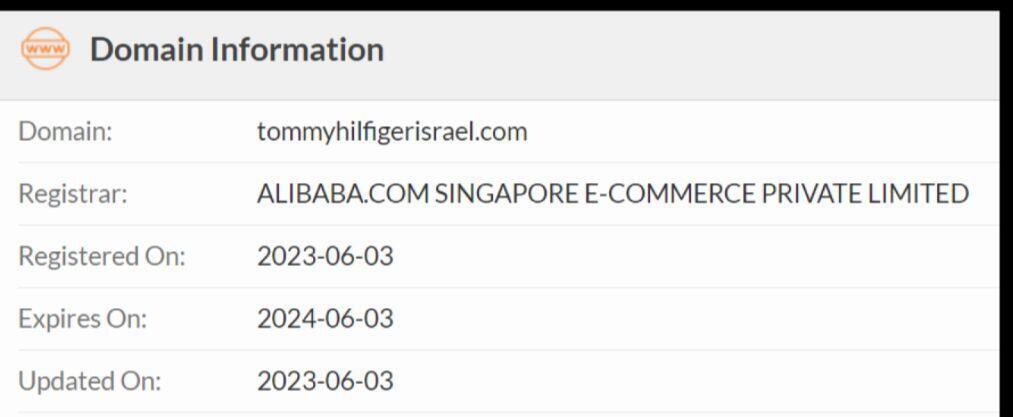
In this particular game of concealment, the Chinese hackers have taken a step up in the sophistication ladder. They've managed to cloak the roots of the faux address so well that even a good old Whois search - the internet's equivalent of a magnifying glass for snooping on website owners - draws a blank on the origin. A quick peek at the real URL, however, leaves no room for doubt - the legitimate owner is indeed the shoe brand.
Mark Ziperstein, an information security researcher at Cybereason who analyzed the campaign, shared with Ynet, "You need to take a closer look at the website. Check out the contact details - are there a valid address and phone number? Info about the company? Can you pick up your order yourself?
"Be suspicious if the site claims to be a well-known, established company but was created recently. Watch out for credit card info asked on a page that isn't secure. Red flags also include not getting a confirmation email after signing up, discounts that seem too good to be true, and lots of spelling and grammar mistakes."
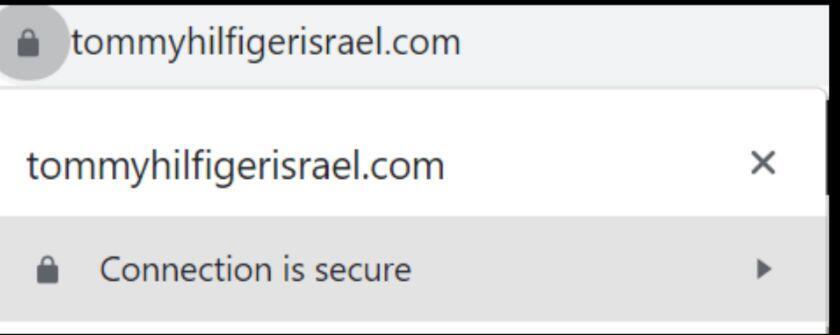
"This is an international operation that has extended its reach to Israel. The deceptive websites are crafted using a similar blueprint, exploiting legitimate online services. Their primary objective could be to pilfer personal data, credit details, and potentially more, paving the way for further attacks. The practice of simply looking for a lock symbol before the URL just doesn't cut it anymore," Ziperstein further notes.
The hackers have a few tricks tucked up their sleeves to lull web surfers into a complacent sense of safety. They serve up websites garnished with a lock symbol or an "https" prefix, essentially the online equivalent of a reassuring pat on the back. This little lock icon assures us that the site is encrypted and playing nice with the security industry.
Plus, these sites are doppelgangers of the real deal, parading around in the original business's name and images. But don't be fooled - while they're dressed to the nines in the brand's finery, they don't deliver the goods. Their real purpose? To pocket your information, sensitive details, and credit card digits.
Adding another layer to this digital masquerade, the page where you're asked to spill your credit card secrets doesn't even name-drop a secure, recognized payment system. The social network links are like misleading detour signs, taking you anywhere but the business's official pages. And the cherry on top? The website popped up fresh out of the oven in 2023, but the owner's identity is hidden like a secret ingredient.
The research also unveils that these sites are elbowing their way to the top of search engine results, sometimes even outshining the original sites. Now, we're not quite sure how these hackers managed to leapfrog over the original websites in this digital game of king of the hill, but one thing's clear - This isn't their first rodeo.
Cybereason has put dozens of these suspect sites on their radar, but there's a good chance there could be even more hidden in the digital landscape. Given the heightened tension in these times of conflict, Israel's network is under extra pressure. The best advice? Be extra careful when considering purchases from sites you're not familiar with.
This doesn't mean every unfamiliar site is a scam, but more often than not, legitimate sites will have clear indicators of authenticity, such as an originating address in Israel (look for a co.il ending or com/il if it's the local version of an international site).
Brands typically have their own exclusive domains. For instance, if you navigate to Nike's official website, the URL would be nike.com, not nikeisrael.com. Official importers also stick to authentic URLs rather than opting for brand names with a localized twist. Take, for example, Reebok's Israel site, which can be found at reebok.co.il.
Interestingly, just four search results down, there's a counterfeit site at reebokisrael.com (it's advisable not to visit it, even out of curiosity, as such sites can sometimes harbor harmful elements). The genuine Puma website for Israel, il.puma.com, is actually operated from Dubai. So, even if you were to look up its origin and find it isn't local, rest assured, it's still the authentic site.