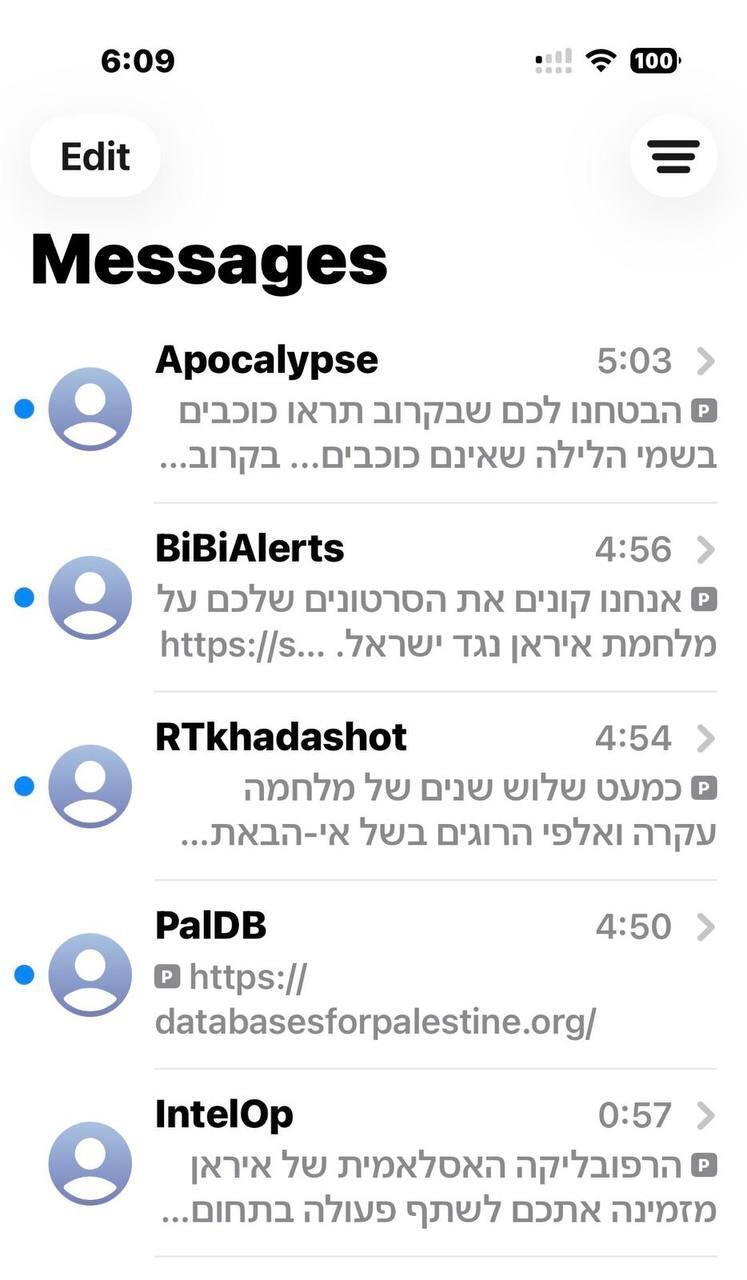
When your phone vibrates at 2 a.m., it is usually a wrong number or a particularly anxious relative. But overnight, for thousands of Israelis, that vibration came courtesy of the ayatollahs’ regime in Tehran. Numerous concerned citizens contacted ynet overnight after receiving alarming messages on their phones, all of them sharing one goal: to sow panic.
The Israel National Cyber Directorate told us it had identified in recent hours a broad influence operation involving threatening text messages with a single objective: to undermine our collective peace of mind and create a sense of digital persecution. In Tehran, it seems, they believe this is the perfect time to build an intimate relationship with Israeli citizens, even if it is based on generic threats sent through mass distribution systems.
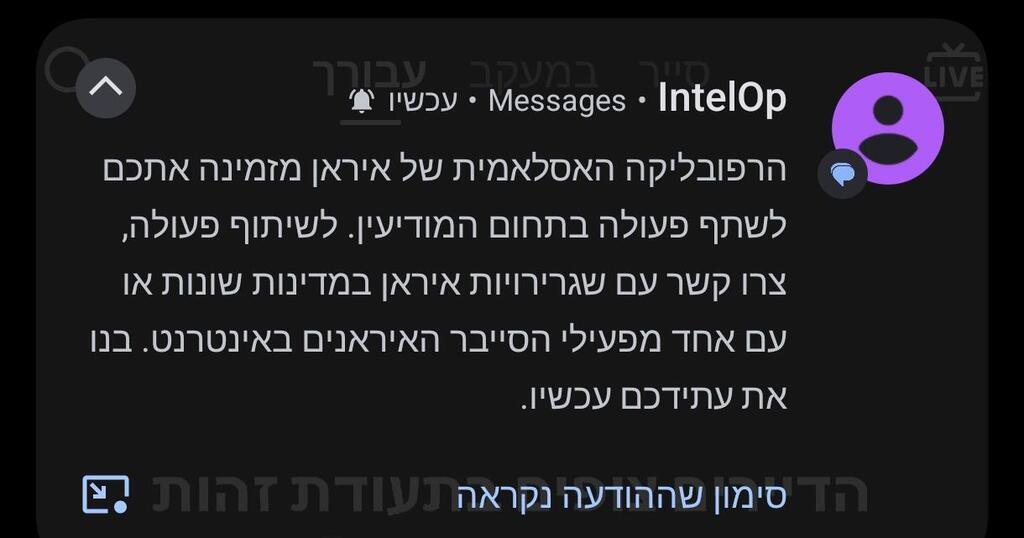
The message sent to Israelis read: “The Islamic Republic of Iran invites you to take part in an action in the intelligence field. To participate in the operation, contact various Iranian embassies or one of the Iranian cyber operators online. Build your future now.”
The method is familiar and frighteningly simple: threatening, dramatic messages that try to push the recipient into acting on emotional impulse. One citizen who experienced the attack told ynet he received six different text messages within just one hour, all from different numbers. Ron Ben-Yishai, ynet’s security analyst, explains that this is not a show of strength but rather an expression of panic on the Iranian side. The attempt to prevent Israel from joining a possible American attack under the Trump administration is leading the Iranians to use cheap, readily available tools to try to influence public morale in Israel.
From a technological standpoint, it is important to distinguish between a “hack” and “harassment.” Merely receiving the text message does not indicate that the phone has been breached or that a private account has been compromised. This is the use of mass distribution systems, or broadcast systems, similar to those used by marketing companies for promotions — except that instead of a pizza coupon, the Iranians are sending you existential threats. These tools, based on bots and distribution lists that were purchased or harvested from old databases, are part of what the intelligence world defines as “cognitive warfare.”
The history of this technology points to a fascinating evolution. The term “cognitive warfare” was first coined around 2017 and has since become a genuine engineering tool. If propaganda in the past was slow, “handmade” work, today, in the age of artificial intelligence and automation, it is a mass production line. The goal is to attack what NATO calls the enemy’s “OODA loop” — observe, orient, decide and act. When a citizen receives such a message, the attacker hopes to cause a “cognitive collapse” — a moment when emotion overrides logic and the individual unknowingly becomes an agent of the enemy by spreading the panic further.
Israel is not alone in this campaign. An examination of other arenas around the world reveals similar patterns. Russia, for example, makes extensive use of such methods in Ukraine, where text messages have been sent encouraging civilians to carry out acts of sabotage or arson in exchange for money or under threat. In China, the “borrowed mouth” strategy in Europe uses bots and influencers to amplify Communist Party messages without leaving official fingerprints. The comparison to past attacks, such as the Russian “Doppelgänger” campaign, shows that the technology has become more effective and cheaper, allowing countries like Iran to run influence operations at the push of a button.
The response to these attacks is primarily digital discipline. The Cyber Directorate’s recommendations are clear: Do not reply to the messages, do not click on attached links and do not forward the messages to family WhatsApp groups. Relying only on official sources is the best defense against these social engineering attempts. Ultimately, this is a battle for consciousness in which technology is only the means; the target is our focus and resilience. When the Iranians try to frighten us in the middle of the night, the best response is probably simply to go back to sleep.