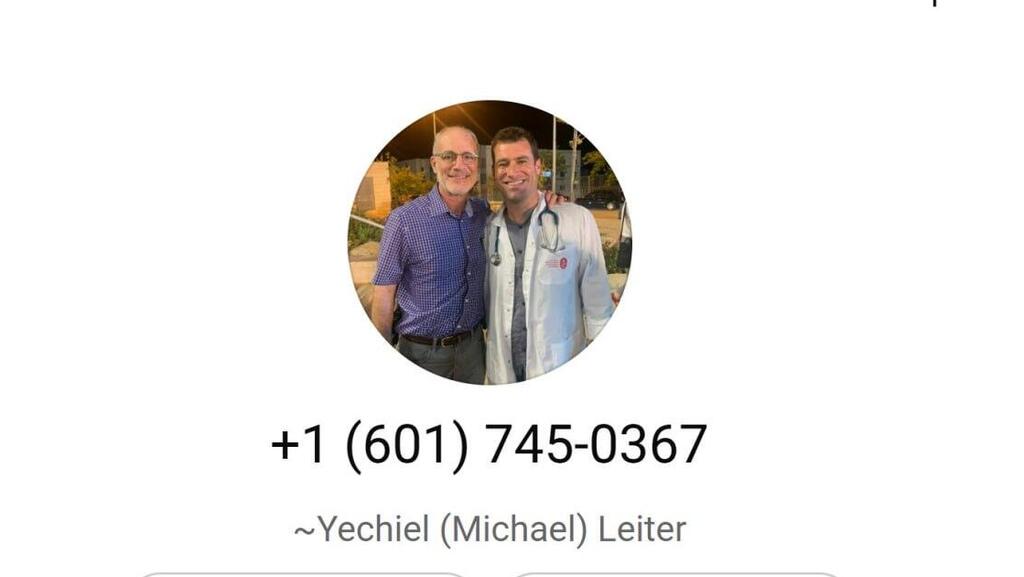
An Iranian agent has recently been impersonating Israel’s ambassador to Washington, Yechiel Leiter, using a photo of his son, Maj. (res.) Moshe Yedidyah Leiter, who was killed in combat in Gaza in November 2023.
Senior officials and journalists, including this reporter, received WhatsApp messages from a U.S. phone number registered under Leiter’s name. The profile picture showed Ambassador Leiter alongside his son, who was killed in the Gaza Strip.
At first glance, the message appeared routine, with “Leiter” seeking to coordinate a meeting for the ambassador. When recipients responded, the sender suddenly identified himself as an aide to the Israeli ambassador and attempted to schedule a meeting by sending a fake Google Meet link.
Those who clicked the link were prompted to enter a username and password, which were then stolen by the attacker.
This is not the first time Iranian agents have attempted to impersonate senior Israeli officials. In a previous case, an Iranian agent posed as Cabinet Secretary Yossi Fuchs and sought to arrange urgent meetings with senior figures. The messages were sent from a number displaying Fuchs’ photo.
The security officer of the Prime Minister’s Office filed a complaint with police, and a warning circulated to government ministries stating that recipients should not cooperate with or respond to the number.
The Shin Bet later exposed correspondence from the agent who impersonated Fuchs, saying the goal was to extract information from senior public servants by gaining access to their digital devices, including email accounts, computers and smartphones.
Among the information sought were home addresses, personal connections and locations frequently visited by targeted individuals. Such details, officials said, could be used in potential attacks against them, including through Israeli cells recruited inside the country.
As part of its operations, the Shin Bet said it had thwarted 85 cyberattacks targeting the devices and computers of Israeli officials.
Iranian approaches are typically carried out via WhatsApp, Telegram or email, using tailored cover stories based on each target’s professional background so the outreach does not appear unusual. The Shin Bet has warned of a significant increase in Iranian phishing attempts in recent months.
“We are seeing continued, relentless attempts by hostile elements in the campaign Iran is waging against Israel to harm public figures,” a Shin Bet official said. “The public is required to remain alert and cautious. These are cyberattacks that can be prevented through awareness, vigilance, suspicion and responsible online behavior, especially by avoiding clicking on unfamiliar links.”