"According to new reports, the power plant in Dimona was attacked by Hamas rockets," "to prevent the destructive effect of poisonous gas, take a potassium iodine tablet": these are the contents of some the messages and emails received in the last day by quite a few Israelis. The messages are sent from unknown email addresses including from Brazil, for example, or in SMS messages impersonating the Color Red rocket warning app, the same app that the hackers already tried to leverage against Israelis last week.
Read more:
At this point, it is not entirely clear who is behind this hacking operation. However, this is a leap forward in terms of capability. It is no longer a case of simple website hacking and vandalism or phishing attempts via SMS, but a combined operation with pre-prepared materials. For example, the hackers even prepared fake screenshots of Israeli news websites, including Ynet. They also set up a website to publicize their successes and scare more Israelis.
The messages were written in garbled Hebrew. It is evident that these are not Hebrew-speakers and appear to have machine translation to prepare the content. The messages are also not very accurate and refer, for example, to a "power plant" in Dimona, or a garbled headline of the fake news . The syntax will not succeed in tricking a native Hebrew speaker, but those for who Hebrew is not their first language may believe the contents.
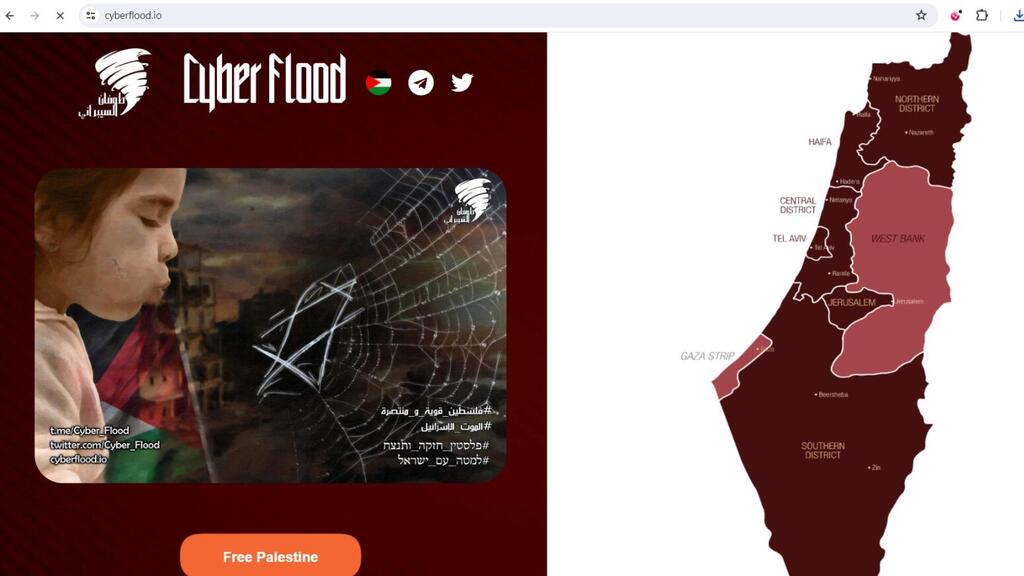
This operation is very reminiscent of similar actions by Russia in recent years. Although it is evident that this is not the work of experts in the field, the influence of the Russians is very evident. For example, combining the sources of information - emails, SMS, website and probably also social networks. At the same time, the group that distributes the content and calls itself CyberFlood, a nickname that connects with the name Hamas gave to the current war (Operation Al-Aqsa Flood), has tried to convince the public that it hacked into the websites of municipalities and local authorities and stole databases with citizens' personal information. An examination revealed that the database uploaded by the hackers to the network was stolen two years ago as part of a hack into several municipal websites, so this is not current information.
Actions of this kind by the hackers are mainly intended to sow panic among the public and to demoralize. But this time, despite the experience that shows a higher capacity than before, it is still an attack that is very difficult to perceive as credible and truly threatening.
Still, the differences are also seen in the combination of the different mediums. If in the past the hackers would send a phishing email or a separate message, now it is a bunch of parallel vectors in all of which you can see the repetition of the message they are trying to convey. On the other hand, the use of databases that, according to Check Point's information, have been circulating on the internet for a long time, indicates that this is not yet an out-of-control arena.
3 View gallery


Pro-Palestinian hackers say they have leaked the personal information of Israeli citizens
(Screenshot: Telegram)
The general recommendation for those who receive such messages is to ignore them and not click on suspicious links that sometimes appear in such messages. These are mainly annoying messages, but they are not dangerous. In general, if you suspect an attempted attack, the recommendation is to contact the 119 hotline of the Israel National Cyber Directorate and report it.
The Israel National Cyber Directorate said in a statement that: "This is a cynical intimidation attempt. We are working to curb the circulation of these messages. We remind you to consume information from official sources and download the official application of the Home Front Command." With regard to the hackers' saying they attacked local municipalities and stole citizen databases, the directorate says that "regarding the municipalities - at this point it looks like recycled information from the City for You event from two years ago."